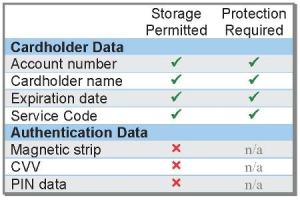
It seems that the CC numbers were saved for logging suspicious and fraudulent transactions. It doesn't make sense to me why they need to store so much information about them (especially since their payment gateway likely has a copy of the data), but the data includes the first 4 digits and last 4 digits of the CC number, the expiration date, the CVV code, and the billing information about the user.
There is another location that contains CC numbers (first 6 digits and last 4 digits), but it seems to be InTrust data from before the Epik acquisition. The transactions are only from 2009 and 2010.
A third location contains full CC numbers, but there are only 16 of them, and they are also from around the same time period.
Speaking of logs, it seems like a huge waste for Epik to store so much information for logging purposes. One table I see has almost 35 million entries. Do they really need to keep detailed logs from over 11 years ago?