Overview of PCI Data Security Standard (PCI DSS)
PCI DSS is the global security standard for all entities that store, process or transmit cardholder data and/or sensitive authentication data. PCI DSS sets a baseline level of protection for consumers and helps reduce fraud and data breaches across the entire payment ecosystem. It is applicable to any organisation that accepts or processes payment cards.
PCI DSS compliance involves 3 main things:
- Handling the ingress of credit card data from customers, namely, that sensitive card details are collected and transmitted securely
- Storing data securely, which is outlined in the 12 security domains of the PCI standard, such as encryption, ongoing monitoring, and security testing of access to card data
- Validating annually that the required security controls are in place, which can include forms, questionnaires, external vulnerability scanning services and 3rd party audits (see the step by step guide below for a table with the four levels of requirements)
Handling card data
Some business models do require the direct handling of sensitive credit card data when accepting payments, while others do not. Companies that do need to handle card data (e.g. accepting untokenised PANs on a payment page) may be required to meet each of the 300+ security controls in PCI DSS. Even if card data only traverses its servers for a short moment, the company would need to purchase, implement and maintain security software and hardware.
If a company does not need to handle sensitive credit card data, it shouldn’t. Third party solutions (e.g. Stripe Elements) securely accept and store the data, whisking away considerable complexity, cost and risk. Because card data never touches its servers, the company would only need to confirm 22 security controls, most of which are straightforward, such as using strong passwords.
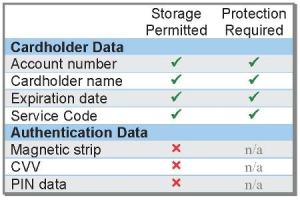
Storing data securely
If an organisation handles or stores credit card data, it needs to define the scope of its cardholder data environment (CDE). PCI DSS defines CDE as the people, processes and technologies that store, process or transmit credit card data – or any system connected to it. Because all 300+ security requirements in PCI DSS apply to CDE, it’s important to properly segment the payment environment from the rest of the business so as to limit the scope of PCI validation. If an organisation is unable to contain the CDE scope with granular segmentation, the PCI security controls would then apply to every system, laptop and device on its corporate network. Yikes!
Annual validation
Regardless of how card data is accepted, organisations are required to complete a PCI validation form annually. The way PCI compliance is validated depends on a number of factors, which are outlined below. Here are 3 scenarios in which an organisation could be asked to show that it is PCI compliant:
- Payment processors may request it as part of their required reporting to the payment card brands
- Business partners may request it as a prerequisite to entering into business agreements
- For platform businesses (those whose technology facilitates online transactions among multiple distinct sets of users), customers may request it to show their customers that they are handling data securely
The latest set of security standards,
PCI DSS version 3.2.1, includes 12 main requirements with over 300 sub-requirements that mirror security best practices.
Build and maintain a secure network and systems- Install and maintain a firewall configuration to protect cardholder data
- Do not use vendor-supplied defaults for system passwords and other security parameters
Protect cardholder data
- Protect stored cardholder data
- Encrypt transmission of cardholder data across open or public networks
Maintain a vulnerability management programme
- Protect all systems against malware and regularly update anti-virus software
- Develop and maintain secure systems and applications
Implement strong access control measures
- Restrict access to cardholder data by business need to know
- Identify and authenticate access to system components
- Restrict physical access to cardholder data
Regularly monitor and test networks
- Track and monitor all access to network resources and cardholder data
- Regularly test security systems and processes
Maintain an information security policy
- Maintain a policy that addresses information security for all personnel
To make it “easier” for new businesses to validate PCI compliance, the PCI Council has created nine different forms or Self-Assessment Questionnaires (SAQs) that are a subset of the entire PCI DSS requirement. The trick is working out which is applicable or whether it’s necessary to hire a PCI Council-approved auditor to verify that each PCI DSS security requirement has been met. In addition, the PCI Council revises the rules every three years and releases incremental updates throughout the year, adding even more dynamic complexity.